Three Pillars. One Mission.
The NexGen Secure curriculum is built on three interlocking concepts — each one essential, each one reinforcing the others across every grade level.
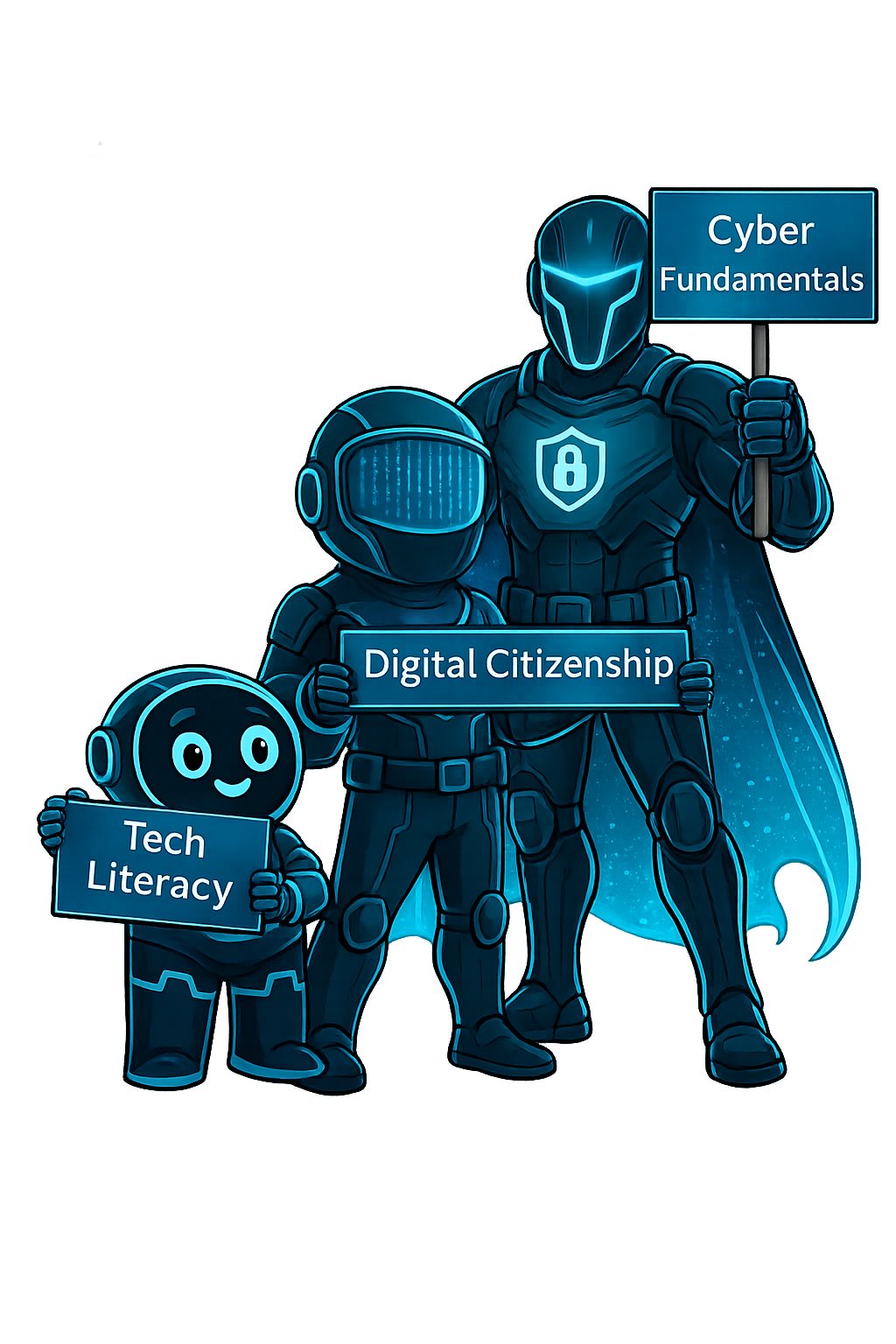
Before students can stay safe online, they need to understand what "online" means — how devices, networks, and the digital world actually work.
How to navigate the digital world with safety, integrity, and responsibility — from protecting personal privacy to standing up against cyberbullying and online harm.
Real-world security skills and the mindset of a defender — building the foundation for a future career in one of the most in-demand fields on the planet.

